Anhangssicherheit implementieren Checklist
Sichern Sie Ihre Farmdaten! Diese umfassende Checkliste führt Sie bei der Implementierung robuster Anbindungs-Sicherheit für die Landwirtschaft und schützt sensible Informationen wie Bodenkarten, Ertragsdaten und Gerätedetails. Steigern Sie die Cybersicherheit Ihres Betriebs und bleiben Sie konform – jetzt herunterladen! #landwirtschaft #cybersicherheit #farmensicherheit #datensicherheit #checklist
Diese Vorlage wurde 2 Mal installiert.
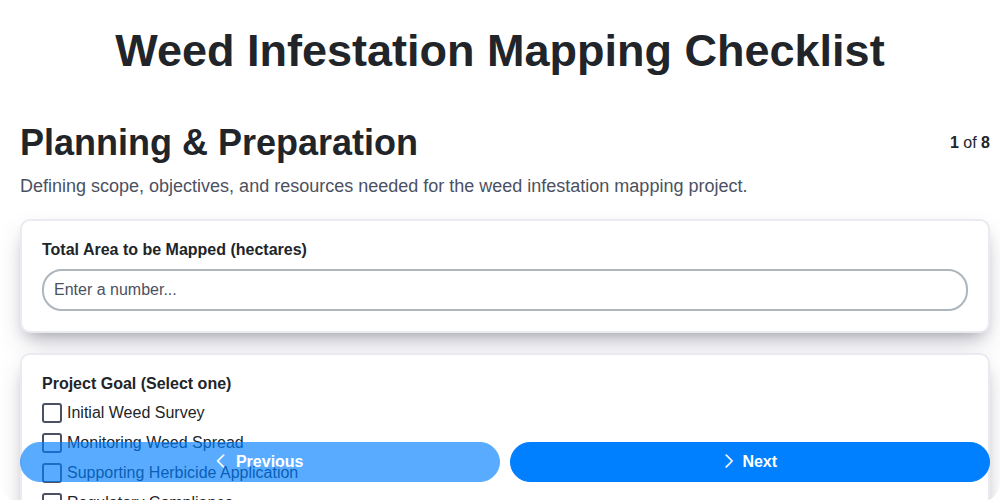
Planung & Anforderungen
Definieren Sie Sicherheitsanforderungen, Compliance-Überlegungen und den Umfang der zu schützenden Anhänge innerhalb der Kategorie Landwirtschaft.
Definieren Sie den Umfang der zu sichernden „landwirtschaftlichen Anhänge“.
Schätzen Sie die Gesamtzahl der im Umfang befindlichen Anhänge.
Identifizieren Sie relevante regulatorische Rahmenwerke (z. B. DSGVO, CCPA, Branchenstandards).
Wählen Sie die Hauptrisiken, die mit unsicheren landwirtschaftlichen Anbauten verbunden sind.
Geplantes Fertigstellungsdatum für die Erstimplementierung.
Akzeptable Aufbewahrungsfrist für Anhänge bestimmen
Anhangsmetadaten und Klassifizierung
Ein System zur Kennzeichnung und Klassifizierung landwirtschaftlicher Anhänge (z. B. Karten, Verträge, Sensordaten, Feldberichte) basierend auf ihrer Sensibilität und regulatorischen Anforderungen einrichten.
Anhänge Sensitivitätsstufe
Kategorien von Daten (z. B. regulierte Daten)
Anhangstyp
Datenursprung/Quelle
Beschreibung/Zweck des Anhangs
Erstellungs-/Hochladedatum
Zugriffssteuerung und Berechtigungen
Implementieren Sie granulare Zugriffskontrollen und definieren Sie, wer landwirtschaftliche Anhänge einsehen, herunterladen, hochladen und ändern kann. Berücksichtigen Sie rollenbasierte Zugriffsrechte und Multi-Faktor-Authentifizierung.
Standard-Zugriffsebene für Anhänge (Neue Anhänge)
Rollen mit Hochladeberechtigungen
Standard-Downloadberechtigung für externe Benutzer
Multi-Faktor-Authentifizierung für den Download erforderlich?
Gruppen mit Zugang zu sensiblen Felddaten (z. B. Bodenanalysen)
Spezifische Zugangsbeschränkungen (z. B. standortbasierte Einschränkungen)
Verschlüsselung & Speicherung
Bestimmen Sie geeignete Verschlüsselungsmethoden (im Ruhezustand und während der Übertragung) für landwirtschaftliche Anhänge. Wählen Sie sichere Speicherlösungen, die die einschlägigen Vorschriften erfüllen.
Verschlüsselungsmethode (Im Ruhezustand)
Verschlüsselungsmethode (Während der Übertragung)
Schlüssel-Rotationsfrequenz (Tage)
Speicherort
Details des Speicheranbieters (falls zutreffend)
Datenredundanzstufe
Zugriffsberechtigungen für Speicher beschreiben
Data Loss Prevention (DLP)
Maßnahmen zur Verhinderung unbefugter Datenlecks umsetzen, wie die Beschränkung von Downloads und die Anwendung von Wasserzeichen.
Download-Berechtigungen einschränken?
Maximale Dateigröße (MB)
Dateitypbeschränkungen
Andere eingeschränkte Dateitypen angeben (falls oben ausgewählt)
Wasserzeichen-Anhänge?
Wasserzeichen-Textinhalt
Redaktion einführen?
Audit & Überwachung
Logging und Monitoring einrichten, um den Zugriff auf Anhänge, Änderungen und mögliche Sicherheitsvorfälle zu verfolgen. Benachrichtigungen für verdächtige Aktivitäten einrichten.
Aufzeichnungsperiode für den Zugriff auf Anhänge (Tage)
Alarmsystem für verdächtige Aktivitäten (z. B. SIEM, E-Mail)
Letztes Sicherheitsaudit des Anhangssystems
Zusammenfassung der jüngsten Prüfungsergebnisse und Abhilfemaßnahmen
Überwachte Anwendungszugriffsereignisse
Häufigkeit der automatisierten Überprüfung von Protokolldaten
Compliance & Rechtliches
Stellen Sie die Einhaltung relevanter Vorschriften (z. B. DSGVO, CCPA, branchenspezifische Datenschutzstandards) in Bezug auf landwirtschaftliche Daten und Anhänge sicher.
Anwendbare Vorschriften identifizieren (z. B. DSGVO, CCPA, USDA-Datenschutzbestimmungen)
Weitere identifizierte Vorschriften angeben (falls zutreffend)
Aufbewahrungsfrist (in Jahren) gemäß Vorschriften
Datum der letzten Überprüfung und Aktualisierung der Datenschutzrichtlinie
Zusammenfassung der Implementierung von Betroffenenrechten (z. B. Auskunftsrecht, Recht auf Löschung)
Ist ein Einwilligungsmanagement-Mechanismus vorhanden?
Datenschutzrichtliniendokument hochladen
Verzeichnis der Verarbeitungstätigkeiten (DPIA/PRA) Dokumentation
Testen & Validierung
Führen Sie umfassende Tests durch, um die Wirksamkeit der implementierten Sicherheitsmaßnahmen zu validieren und etwaige Schwachstellen zu identifizieren.
Anzahl der durchgeführten Testfälle
Testumgebung
Testresultate-Dokumentation hochladen
Zusammenfassung der gefundenen Sicherheitslücken (sofern vorhanden)
Abgedeckte Testbereiche (alle zutreffenden auswählen)
Datum des letzten Sicherheitsscans
Anzahl der Anhänge Getestet
Schulung und Sensibilisierung der Benutzer
Schulen Sie Benutzer in sicheren Verfahren zur Handhabung von Anhängen und der Bedeutung der Datensicherheit.
Haben Sie die Richtlinie zur Sicherheit landwirtschaftlicher Daten überprüft?
Beschreiben Sie kurz Ihr Verständnis für die Bedeutung des sicheren Umgangs mit Bindungen.
Sind Sie mit der Identifizierung von Phishing-Versuchen im Zusammenhang mit landwirtschaftlichen Daten vertraut?
Welche der folgenden gelten als Best Practices beim Umgang mit sensiblen Anhängen?
Datum des Abschlusses der Schulung
Haben Sie Fragen zum sicheren Umgang mit Anhängen? Wenn ja, bitte erläutern Sie diese.
War diese Checklisten-Vorlage hilfreich?
Demonstration der Managementlösung für die Landwirtschaft
Der Betrieb eines Bauernhofs oder eines landwirtschaftlichen Unternehmens ist komplex. ChecklistGuro's Work OS Plattform vereinfacht Ihre Abläufe, von der Anbauplanung und Bewässerungsmanagement bis hin zur Tierverfolgung und Ernteplanung. Erhöhen Sie die Effizienz, reduzieren Sie Abfall und steigern Sie die Erträge! Sehen Sie, wie ChecklistGuro Ihr landwirtschaftliches Unternehmen revolutionieren kann.
Ähnliche Checklisten-Vorlagen
Gemeinsam schaffen wir das
Benötigen Sie Hilfe bei Checklisten?
Haben Sie eine Frage? Wir helfen Ihnen gerne. Bitte senden Sie uns Ihre Anfrage, und wir werden Ihnen umgehend antworten.