Healthcare Cybersecurity Incident Response Checklist
Minimize disruption and protect patient data. This Healthcare Cybersecurity Incident Response Checklist provides a step-by-step guide to effectively handle breaches, ensuring rapid recovery and continuous compliance. Download now for peace of mind.
Detection & Identification
Initial steps to recognize and confirm a potential cybersecurity incident.
Date of Suspected Incident
Time of Suspected Incident
Initial Detection Method
Description of Initial Alert/Observation
Affected System(s) - Initial Assessment
Severity Score (if applicable)
Potential Indicators of Compromise (IOCs)
Containment
Actions to limit the scope and impact of the incident.
Affected System Type
Compromised Services
Number of Affected Users (Estimate)
Date System Isolated
Time System Isolated
Detailed Description of Isolation Actions
Isolation Method
Eradication
Removing the threat actor, malicious code, or vulnerability from the system.
Description of Malware/Threat Actor
Number of Affected Systems Initially
Compromised System Roles (e.g., Server, Workstation)
Malware Sample (if available)
Detailed Removal Steps Performed
Date Eradication Steps Completed
Time Eradication Steps Completed
Recovery
Restoring affected systems and data to normal operation.
System Restoration Start Date
System Restoration Start Time
Number of Affected Systems Restored
Detailed Description of Restoration Process
Data Integrity Verification Method
Date of Full System Validation
Signature of Recovery Team Lead
Post-Incident Activity
Reviewing the incident, documenting lessons learned, and implementing corrective actions.
Detailed Incident Narrative
Estimated Financial Impact (USD)
Root Cause Categories
Date of Incident Report Completion
Proposed Corrective Actions
Action Plan Status
Supporting Documentation (Logs, Screenshots)
Communication & Reporting
Internal and external communication protocols and reporting requirements.
Incident Severity Level
Summary of Communication Actions Taken
Number of Individuals Notified (Internal)
Number of Individuals Notified (External)
Date of Initial Notification
Time of Initial Notification
Primary Communication Channel Used
Notes on Communication Effectiveness
Legal & Regulatory Compliance
Ensuring adherence to relevant laws, regulations, and contractual obligations (e.g., HIPAA breach notification).
Breach Notification Triggered?
Date of Breach Discovery
Estimated Number of Records Affected
Summary of Legal Consultation Performed
State Breach Notification Laws Applicable?
Documentation of Legal Review
Description of steps taken to comply with HIPAA Breach Notification Rule
¿Le resultó útil esta plantilla de lista de verificación?
Demostración de la Solución de Gestión de la Atención Médica
¿Está buscando optimizar las operaciones de atención médica y mejorar la atención al paciente? La plataforma Work OS de ChecklistGuro simplifica todo, desde la programación de pacientes y la facturación hasta el cumplimiento normativo y la gestión del personal. Mejore la eficiencia, reduzca la carga administrativa y concéntrese en lo que más importa: sus pacientes. ¡Aprenda cómo ChecklistGuro puede transformar su organización de atención médica!
Plantillas de listas de verificación relacionadas
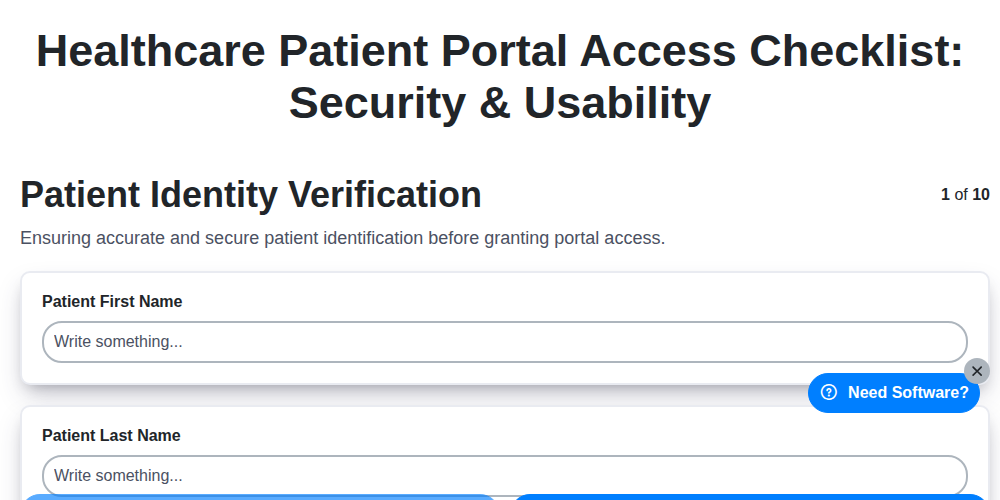
Healthcare Patient Portal Access Checklist: Security & Usability
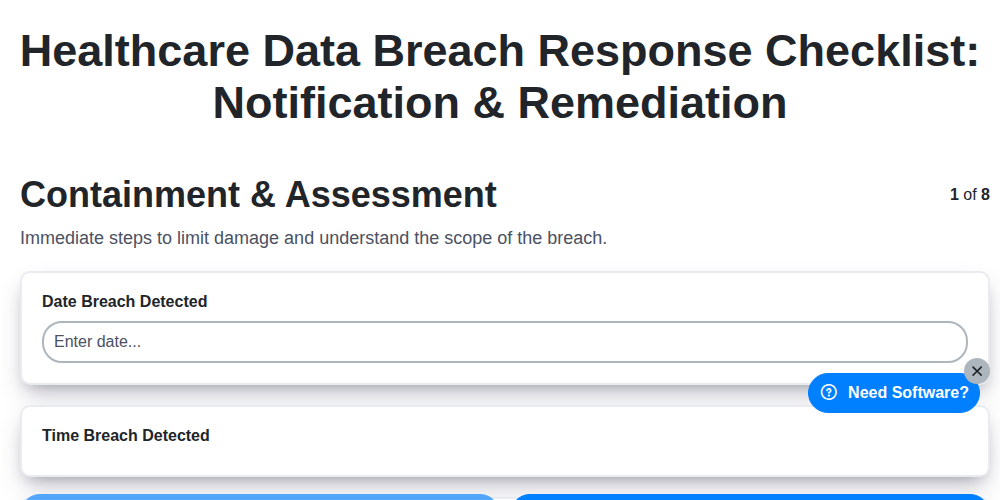
Healthcare Data Breach Response Checklist: Notification & Remediation

Healthcare IT Security Checklist: Data Protection & Access Control
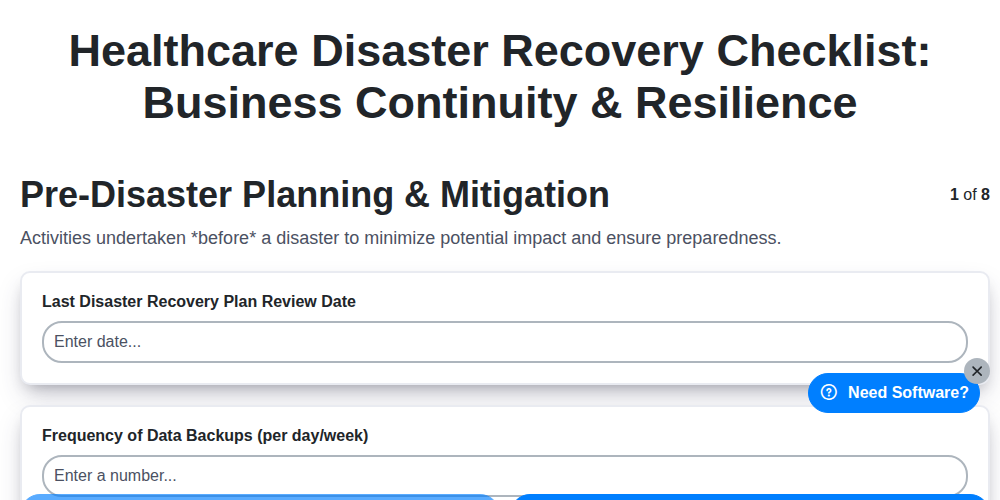
Healthcare Disaster Recovery Checklist: Business Continuity & Resilience
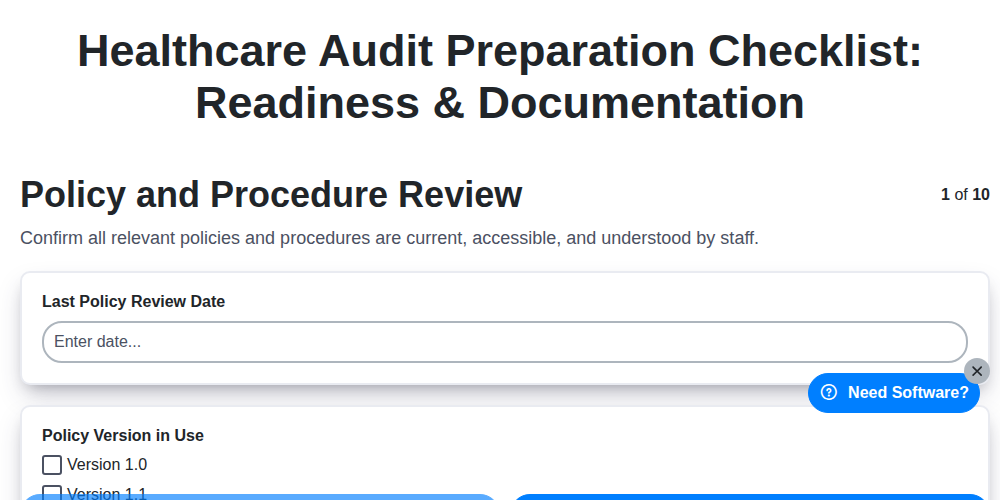
Healthcare Audit Preparation Checklist: Readiness & Documentation
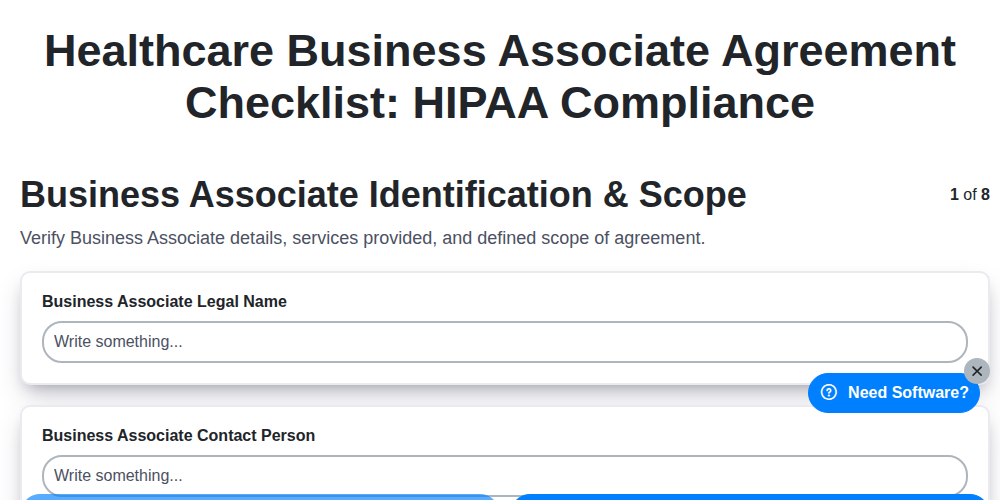
Healthcare Business Associate Agreement Checklist: HIPAA Compliance
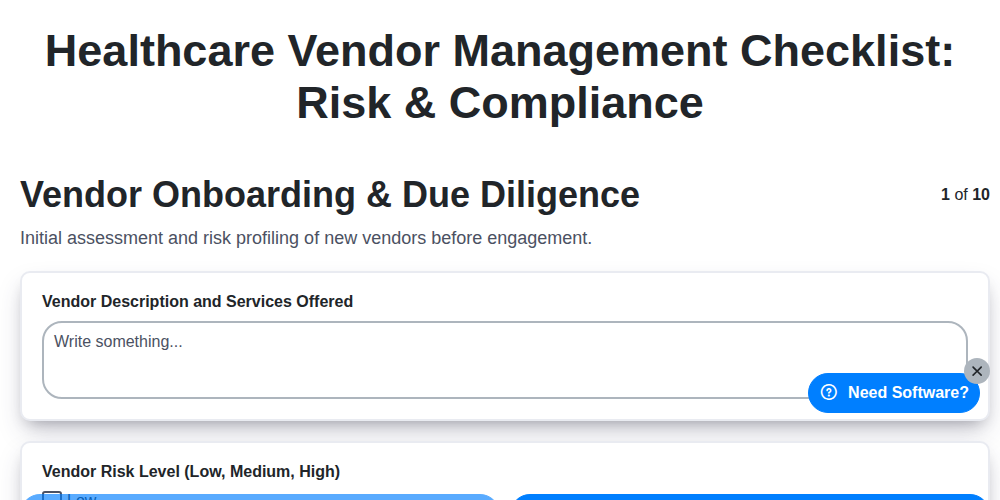
Healthcare Vendor Management Checklist: Risk & Compliance

Healthcare Patient Experience Checklist: Satisfaction & Feedback
Podemos hacerlo juntos
¿Necesita ayuda con las listas de verificación?
¿Tienes alguna pregunta? Estamos aquí para ayudarte. Envía tu consulta y te responderemos a la brevedad.