Cybersecurity Incident Response Plan Checklist
Protect your supply chain! Download our Cybersecurity Incident Response Plan checklist for Logistics. Ensure business continuity, mitigate risks & safeguard your data in the face of cyberattacks. Stay ahead of threats - get your checklist now!
Ce modèle a été installé 3 fois.
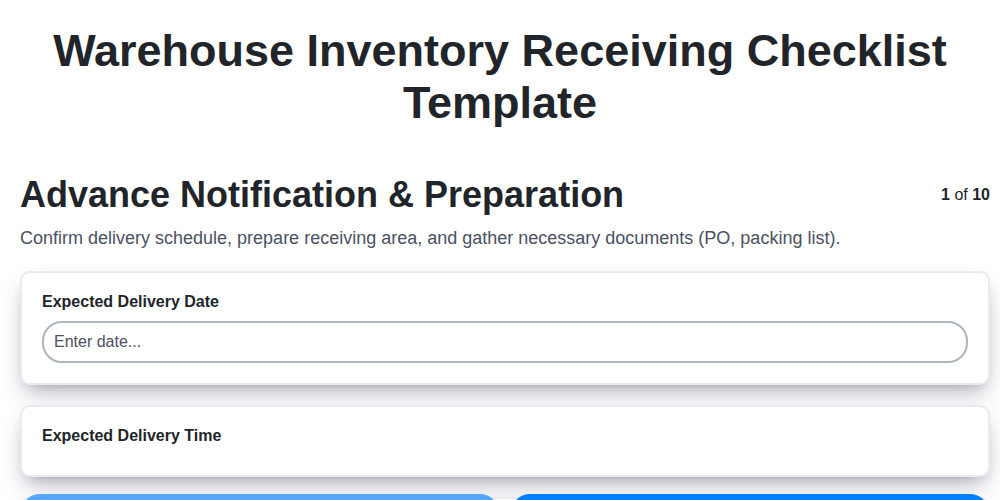
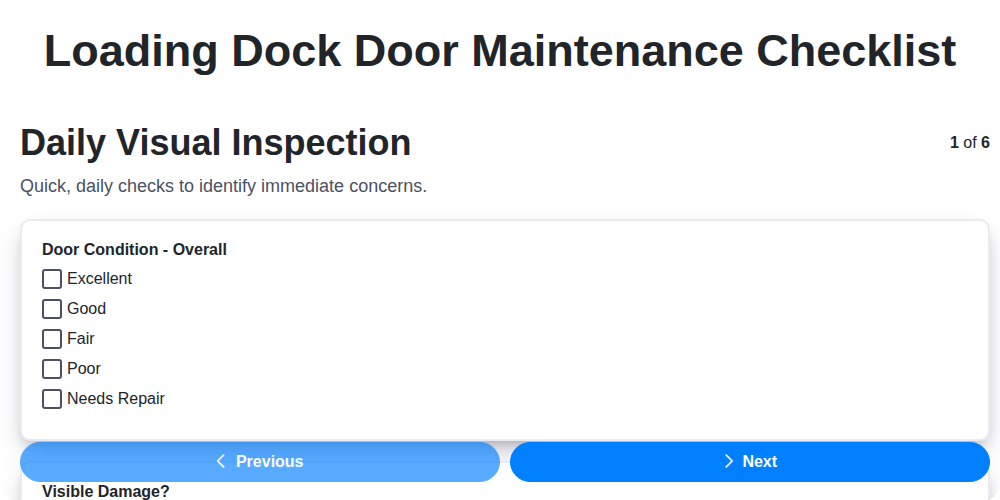
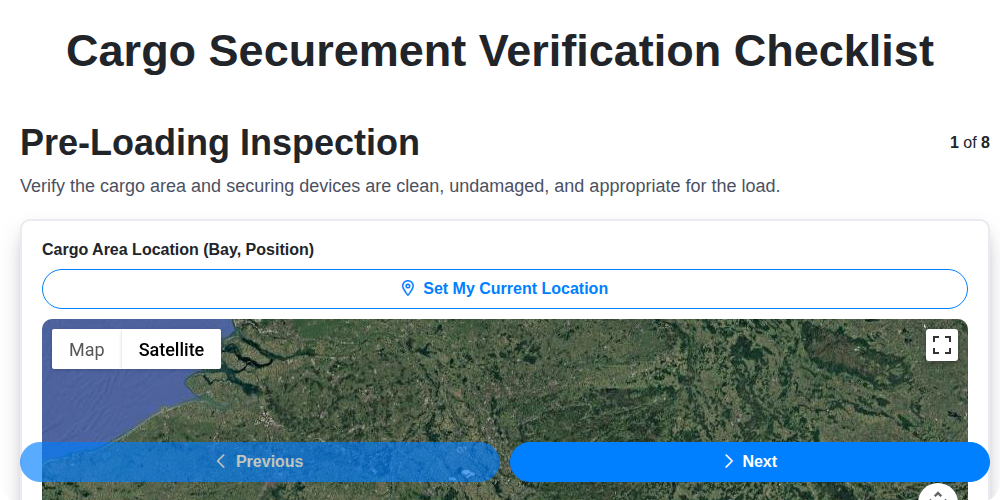
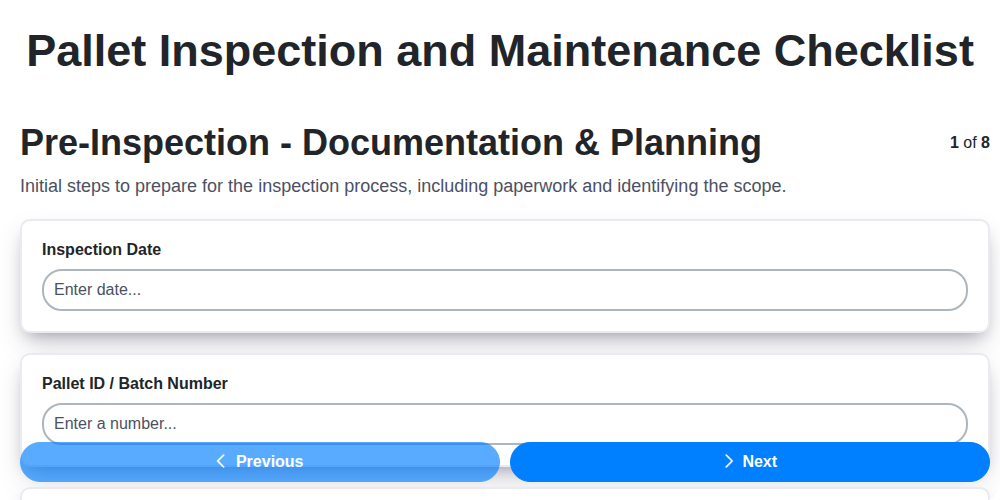
Preparation & Planning
Establishing foundational elements and processes before an incident occurs. Focuses on team setup, asset identification, and risk assessment.
Define Scope of the Incident Response Plan (Logistics Specific)
Maximum acceptable downtime for critical logistics systems (hours)
Primary Incident Response Team Lead Designation
Critical Logistics Systems to be included in the plan (select all that apply)
Asset Inventory List (Logistics Specific)
Date of Last Incident Response Plan Review/Update
Define Roles and Responsibilities of Incident Response Team Members
Detection & Analysis
Procedures for identifying, triaging, and analyzing potential cybersecurity incidents. Includes monitoring, alerting, and initial assessment.
Initial Incident Severity Level (Based on Initial Assessment)
Detailed Description of the Suspicious Activity/Event
Estimated Number of Systems Potentially Affected
Potential Affected Systems/Assets (Check all that apply)
Relevant Logs or Screen Captures (if available)
Date of Initial Detection
Time of Initial Detection
Source System/Log Where Incident Was Detected
Containment & Eradication
Steps to limit the scope of an incident and eliminate the threat. Addresses isolation, system shutdown, and malware removal.
Incident Containment Strategy
Affected Systems/Services to Isolate
Detailed Description of Isolation Procedures
Number of affected systems/devices
Evidence Preservation Strategy (e.g., disk imaging, memory dumps)
Malware Removal Method
Recovery & Restoration
Actions to return affected systems and data to normal operation. Focuses on data restoration, system rebuilding, and verification.
Time to Recovery (RTO) Target
Recovery Point Objective (RPO) Target
Last Successful Data Backup Date
Estimated time to restore core logistics systems
Detailed Restoration Procedures for TMS (Transportation Management System)
Detailed Restoration Procedures for WMS (Warehouse Management System)
Verification steps to confirm data integrity after restoration
Systems Requiring Prioritized Restoration
Post-Incident Activity
Activities performed after the incident is resolved. Includes lessons learned, plan updates, and communication.
Detailed Incident Timeline Review
Lessons Learned - Identify Contributing Factors
Specific Recommendations for Improvement (Based on Lessons Learned)
Estimated Financial Impact (USD)
Date of Plan Update/Review
Summary of Changes Made to the Incident Response Plan
Overall Effectiveness Rating (1-5, 5 being highest)
Logistics-Specific Considerations
Specific actions and controls needed due to the unique aspects of logistics operations (e.g., tracking systems, GPS data, driver devices).
GPS Tracking System Vulnerability Assessment
Critical Data Types at Risk (e.g., shipment manifests, route information, driver details)
Number of Driver Devices (e.g., smartphones, tablets) Managed
Primary Method of Communication with Drivers During an Incident
Potential Impact of Compromised Fleet Management Software
Last Review of Third-Party Logistics Provider Cybersecurity Assessments
Types of Data Stored on Driver Devices (e.g., ELD data, delivery confirmations, route planning)
Contact Person for Immediate Issues Related to Fleet Management Systems
Communication & Reporting
Procedures for internal and external communication throughout the incident response process. Includes stakeholder notification and regulatory reporting.
Incident Severity Level (Initial Assessment)
Initial Incident Summary (for internal documentation)
Primary Communication Method (Internal)
Legal Counsel Notification Required?
Estimated Number of Affected Systems/Locations (Initial)
Date of Incident Report Submission
Time of Incident Report Submission
Which stakeholders need to be notified?
Summary of External Communication (if applicable)
Ce modèle de liste de contrôle vous a-t-il été utile ?
Démonstration de la solution de gestion de la logistique
Fatigué des retards d'expédition, des colis perdus et des itinéraires inefficaces ? La plateforme Work OS de ChecklistGuro rationalise l'ensemble de vos opérations logistiques, de la gestion des entrepôts et de l'exécution des commandes à l'optimisation des itinéraires et au suivi des livraisons. Obtenez une visibilité en temps réel, réduisez les coûts et améliorez la satisfaction client. Découvrez comment ChecklistGuro peut transformer votre entreprise de logistique !
Modèles de liste de contrôle associés
Nous pouvons le faire ensemble
Besoin d'aide avec les listes de contrôle?
Vous avez une question ? Nous sommes là pour vous aider. Veuillez soumettre votre demande et nous vous répondrons rapidement.