Cybersecurity Incident Case Management Checklist Template
Respond swiftly and confidently to cybersecurity threats with our Cybersecurity Incident Case Management Checklist Template. Streamline your response process, ensure compliance, and minimize damage - all in one easy-to-use checklist. Download now and fortify your defenses!
This Template was installed 1 times.
Detection & Reporting
Initial steps after a potential incident is identified.
Date of Detection
Time of Detection
Detection Method
Initial Description of Incident
Severity Score (if applicable)
Reported By
Containment
Actions to limit the scope and impact of the incident.
Affected System(s) Tier
Systems Isolated
Number of Systems Isolated
Isolation Start Date
Isolation Start Time
Containment Actions Description
Isolation Zone Location
Eradication
Removing the root cause of the incident.
Root Cause Analysis Summary
Vulnerability Exploited (if applicable)
Number of Affected Systems
Malware Sample (if applicable)
Remediation Steps Taken
Patch Status (for Affected Systems)
Recovery
Restoring affected systems and data.
System Restoration Start Date
System Restoration Start Time
Percentage of Systems Recovered
Detailed Description of Recovery Actions Taken
Data Integrity Verification Method
Data Verification Completion Date
Description of any Data Loss or Corruption
Post-Incident Activity
Reviewing the incident, documenting lessons learned, and improving security posture.
Summary of Incident Root Cause
Detailed Timeline of Events
Affected Systems/Assets
Estimated Financial Impact ($)
Date of Post-Incident Review
Recommendations for Improvement
Incident Severity Level (Reassessed)
Legal & Compliance
Tasks related to legal requirements, reporting obligations, and data privacy.
Applicable Data Breach Laws?
Specific Legal/Regulatory Requirements?
Date of Legal Consultation?
Estimated Number of Affected Individuals
Notification Requirements?
Summary of Legal Review and Advice
Legal Consultation Documentation
Communication
Internal and external communications related to the incident.
Communication Method
Initial Communication Draft
Stakeholders to Notify
Date of First Communication
Time of First Communication
Contact Person Details (Recipient)
Evidence Preservation
Steps to preserve forensic evidence for investigation.
Date and Time of Evidence Collection
Exact Time of Evidence Collection
Location of Evidence Found
Detailed Description of Evidence
Photos/Screenshots of Evidence
Signature of Evidence Collector
Chain of Custody Record Number
Found this Checklist Template helpful?
Case Management Solution Demo
Streamline your casework & improve outcomes! ChecklistGuro centralizes case details, tasks, & communication. Enhance efficiency, ensure compliance, & deliver exceptional service. Manage it all with our Work OS.
Related Checklist Templates
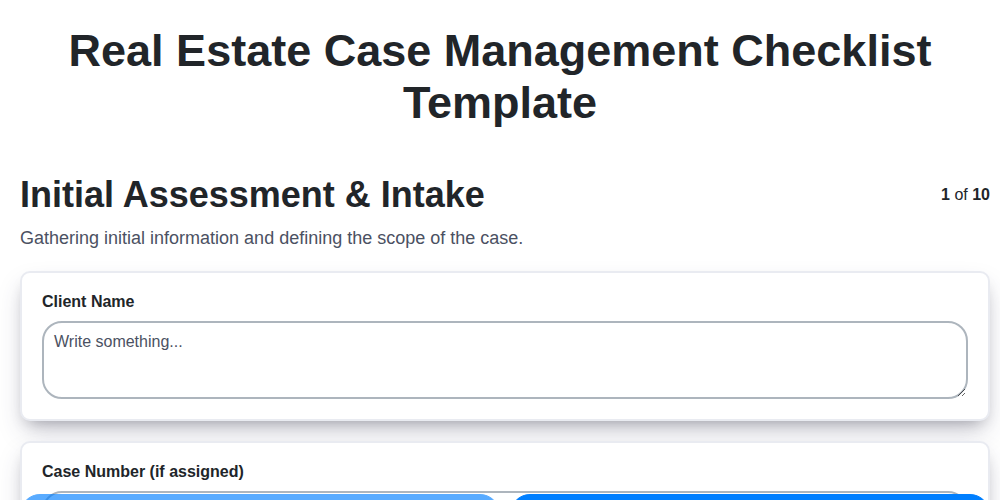
Real Estate Case Management Checklist Template
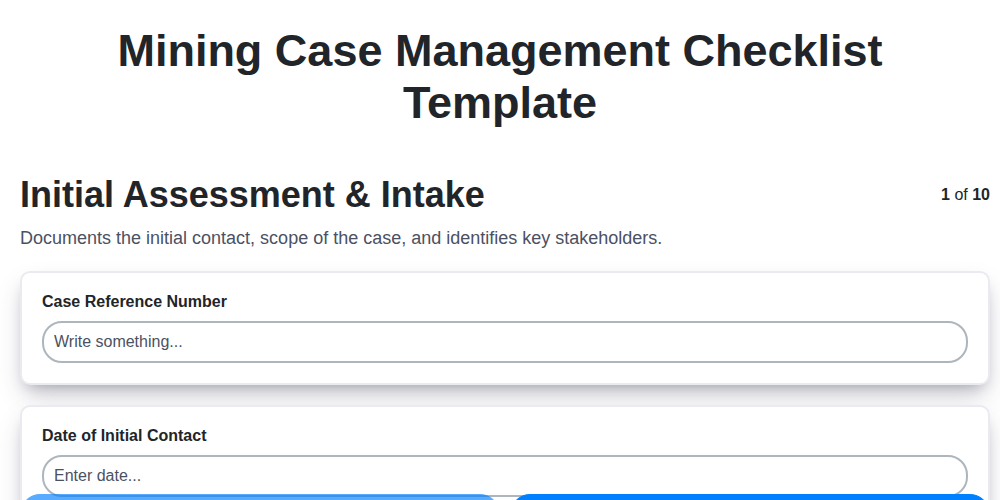
Mining Case Management Checklist Template
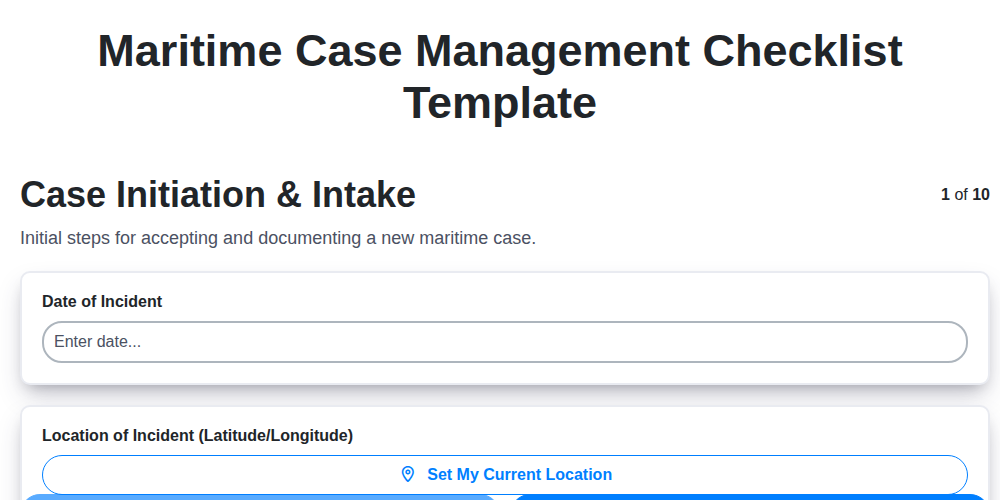
Maritime Case Management Checklist Template

Aviation Case Management Checklist Template
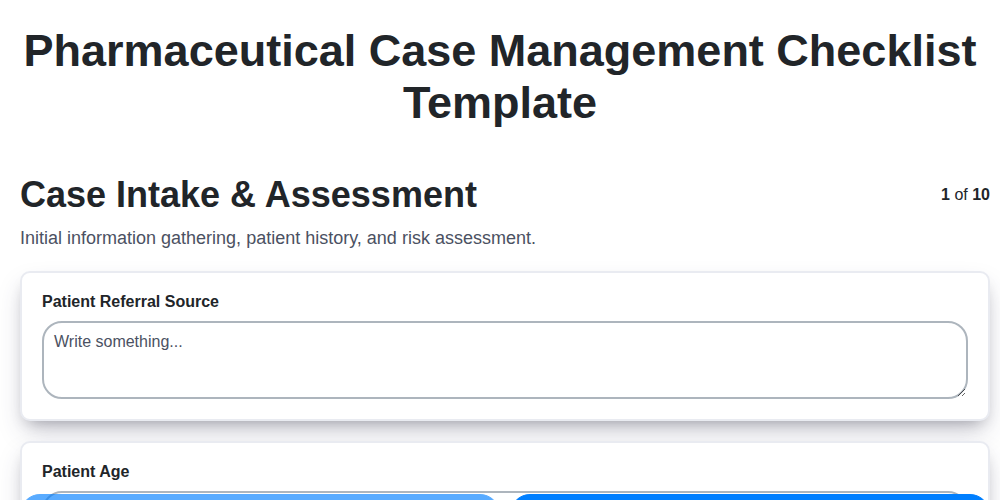
Pharmaceutical Case Management Checklist Template
Intellectual Property Case Management Checklist Template

Product Liability Case Management Checklist Template
Veterans Case Management Checklist Template
We can do it Together
Need help with
Case Management?
Have a question? We're here to help. Please submit your inquiry, and we'll respond promptly.